Did you recently introduce a new password policy barely anyone in your organisation seems to grasp? Beyond the tech know-how, there is an often-overlooked skill that defines great IT leaders – the ability to communicate efficiently. Learn how to best communicate information security changes - from employees to C-level executives - and find the best approach for management buy-in.
1. How to introduce IT changes to employees
Changes in the IT infrastructure, policies (such as password policies) and training around the cybersecurity landscape and how to act compliantly are key tasks to keep the organisation safe and communicating them to the broader organisation is of utmost importance.
When communicating with employees, the IT team must remember that most people are not experts; therefore, all technical jargon should be avoided. Implementing workshops and open sessions is an effective strategy for ensuring employees are clear on expectations and receive information in an easily understood format.
IT leaders should consider taking action beyond written documentation and policies, such as workshops and training on critical topics. This is especially important for organisations handling highly sensitive data or operating in industries with a high risk of cyber attacks.
How FRÄNKISCHE navigated through a cyber attack in 2021 and recognised the importance of information security:

In order to be able to play the desired video, you agree that a connection to the servers of YouTube, LLC, 901 Cherry Ave, San Bruno, CA 94066, USA is established. This transmits personal data (device and browser information (in particular the IP address and operating system) to the operator of the portal for usage analysis.
You can find more information about the handling of your personal data in our privacy policy.
Communication with employees should prioritise education and empowerment, teaching them to identify and avoid risks. For instance, following a phishing test, IT leaders can share the test results, highlighting the number of employees who clicked on the malicious email and providing guidance on how to detect and safeguard against such attacks.
While employees need to understand the significance of cybersecurity training and exercise, they may not need to grasp the broader risk landscape, which is more relevant for C-level executives.
2. How to communicate with fellow leaders
IT leaders often need assistance from department heads to complete their projects, whether it is a simple question about a new phone system or gaining insights into internal processes to complete an Information Security Audit.
Unlike the rest of the company, IT leaders must carefully explain the “why” behind their requests for information and time when communicating with department heads. Team leads, and managers are often under immense pressure to complete their own tasks and have limited free time. To get their support, IT leaders should thoroughly articulate the overarching reason for their requests and connect them to the company’s business goals and potential risks. This approach will foster greater understanding and cooperation from these key stakeholders.
3. How to approach C-level executives
Communication with C-level executives demands a more business-driven approach, as they are primarily concerned with strategic initiatives, business impact, and risk mitigation strategies.
Given the vast array of responsibilities they manage daily, communication must be clear, concise, and direct, emphasising cost-related aspects and quantitative data. To capture their interest in the overarching risk profile of the company, it is essential to be prepared with the right KPIs relevant to C-level executives.
Discussing business impact and strategic initiatives
Heads of IT might find themselves talking with C-levels about business impact to demonstrate the value of the IT department. Here, IT leaders deep dive into the impact of IT strategies and how those directly lead to revenue growth, cost reduction or operational efficiency. For this, we recommend preparing quarterly meetings and reports that highlight the direct impact of the IT initiatives and clearly demonstrate the impact on revenue and cost-effectiveness through KPIs.
Talking risk management
IT leaders will also find themselves discussing risk management with C-levels and board members. These conversations will primarily focus on the company’s current risk exposure and the potential financial impact of any potential security breaches or disruptions.
IT leaders should report on the organisation’s current risk exposure, the threat landscape and the action plan to mitigate risks and reduce their impact on business operations. In these conversations, IT leaders should highlight the results of past risk audits and provide information regarding the cost and impact of those risks in the business if things were to go sideways.
For example, suppose business operations were to cease due to a cyber-attack or any other risk. In this case, C-levels need to know how that would affect the business operations, what areas would be affected, what the cost would be and how long it would take to recover the business activity. For these reasons, it is of utmost importance that companies have a Business Continuity and Disaster Recovery Plan that is continuously reviewed and shared with higher-level executives.
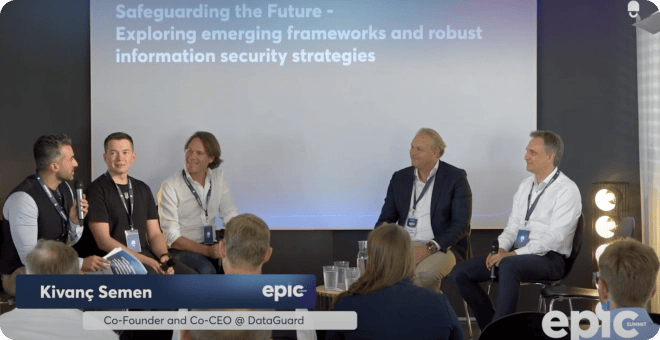
C-level executives place a high emphasis on safeguarding their organisation's future:
In order to be able to play the desired video, you agree that a connection to the servers of YouTube, LLC, 901 Cherry Ave, San Bruno, CA 94066, USA is established. This transmits personal data (device and browser information (in particular the IP address and operating system) to the operator of the portal for usage analysis.
You can find more information about the handling of your personal data in our privacy policy.
IT leaders should also keep asking for leadership's feedback regarding the organisation’s risk appetite and adjust the measures accordingly. For this, we recommend conducting bi-annual workshops to review potential risks, ongoing efforts, and incident response protocols, especially those requiring C-level involvement and responsibility.
Finally, with new legislation and directives such as the NIS2 directive, it is crucial that leaders are aware of the role they play in ensuring Information Security and how they should act if an incident were to be reported.
4. How to communicate with board members and investors
Communication with board members and investors follows a similar line to those of the C-level and executive regarding keeping the focus strategic instead of operational. IT Leaders should focus on the financial implications of IT investments, for example, investing in a new certification such as ISO 27001 and stating the ROI and payback time. IT Leaders should also share compliance and security reports detailing regulatory changes, audit results and new risks.
Share a quarterly compliance and security report detailing any regulatory changes, recent audits, and cybersecurity measures in place.
Key takeaways
In conclusion, by tailoring communication approaches to different stakeholders, fostering transparency, and linking IT initiatives to broader business objectives, heads of IT can play a pivotal role in driving organisational success. After all, in the realm of IT, mastering the art of communication is a catalyst for innovation, collaboration, and sustainable growth.
Do you have unanswered questions about the topic? Don't hesitate to reach out to us for a free consultation.










