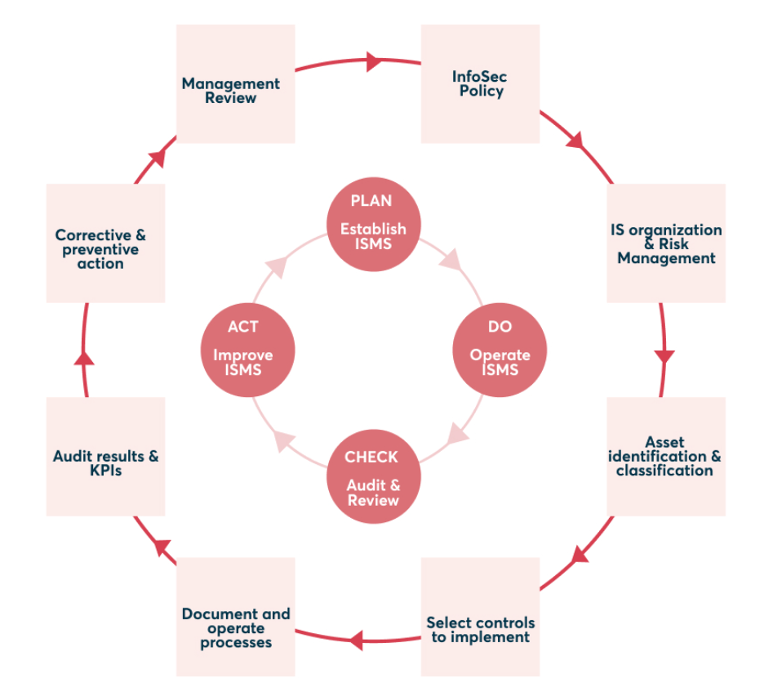
ISO 27001:2022 Controls: What measures are included in Annex A?
The controls outlined in ISO 27001 Annex A are the measures the standard provides to empower businesses in significantly reducing risks. The selection of measures by an organisation is determined based on previously identified risks. Using this foundation, the focus is established, and relevant categories are chosen.
As of 2022, there are a total of 93 controls divided into four categories. Eleven of these controls were newly added to ISO 27001 in 2022. The four categories each describe the focus area of the controls' application.
ISO 27001:2022: Eleven new controls
Since 2022, ISO 27001 has incorporated eleven new controls, each assigned to distinct categories:
A.5.7 Threat intelligence
The "Threat intelligence" measure obligates companies to collect data on potential threats to information security and subject it to in-depth analysis.
A.5.23 Information security for the use of cloud services
Following the "Information security for the use of cloud services" measure, companies are urged to establish and manage information security for the utilisation of cloud services.
A.5.30 ICT readiness for business continuity
Companies must create an ICT continuity plan to maintain operational resilience, fulfilling the "ICT-readiness for business continuity" measure.
A.7.4 Physical security monitoring
Companies need to employ suitable monitoring tools for the "Physical security monitoring" measure to detect and prevent external and internal intrusions.
A.8.9 Configuration management
During "Configuration management," companies must establish guidelines for the documentation, implementation, monitoring, and review of configurations across their entire network.
A.8.10 Information deletion
The document "Information deletion" contains instructions for managing data deletion to comply with laws and regulations.
A.8.11 Data masking
"Data masking" provides techniques for masking personal identifiable information (PII) to comply with laws and regulations.
A.8.12 Data leakage prevention
Following the "Data leakage prevention," companies must take technical measures to detect and prevent the disclosure and/or extraction of information.
A.8.16 Monitoring activities
The "Monitoring activities" measure provides guidelines to enhance network monitoring activities to detect anomalous behaviour and respond to security events and incidents.
A.8.23 Web filtering
Companies must enforce access controls and measures for "Web filtering" to restrict and control access to external websites.
A.8.28 Secure coding
Companies are mandated to implement best practices of secure coding to prevent vulnerabilities caused by inadequate coding methods.
Controls according to ISO 27001: The four categories
The ISO 27001:2022 standard contains 93 controls, which are assigned to four categories: organisational, people, physical, and technological. The grouping of controls into four thematic areas helps organisations to decide who is responsible for implementing the measures and which measures are relevant to the context of the organisation. Each category can be assigned to a specific focus area within your organisation. This makes it easier to apply the relevant controls selectively to your organisation.
Organisational controls (37 measures)
These controls are applicable when the risks do not fall under the topics of people, technology, or physical security. They include, for example, identity management, responsibilities, and evidence collection.
New organisational controls include:
- 5.7: Threat intelligence
- 5.23: Information security for the use of cloud services
- 5.30: ICT readiness for business continuity
Threat intelligence is a significant innovation in this area. This measure goes beyond the detection of malicious domain names. Threat analysis helps organisations better understand how they can be attacked and take appropriate precautions.
People controls (8 measures)
Remote work is a hot topic in the people area. However, the restructuring of the working world also comes with risks. This is where the people measures of ISO 27001 come in. The area related to personnel only includes eight controls. These focus on how employees handle sensitive information during their daily work. This includes topics such as remote work, non-disclosure agreements, and screenings. In addition, onboarding and offboarding processes and responsibilities for reporting incidents are relevant.
Physical controls (14 measures)
Physical controls include security monitoring, maintenance, facility security, and storage media. This category is about how you protect yourself against physical and environmental threats such as natural disasters, theft, and intentional destruction.
New physical controls include:
- 7.4: Physical security monitoring
Technological controls (34 measures)
Technology must also be properly secured to protect information. Technological controls, therefore, deal with authentication, encryption, and data leakage prevention. This can be achieved through various approaches, such as access rights, network security, and data masking.
New technological controls include:
- 8.1: Data masking
- 8.9: Configuration management
- 8.10: Information deletion
- 8.12: Data leakage prevention
- 8.16: Activity monitoring
- 8.23: Web filtering
- 8.28: Secure coding
One innovation in this area is particularly important: data leakage prevention. Web filtering is also helpful: This control describes how organisations should filter online traffic to prevent users from visiting potentially harmful websites.